Products
-



$5,000.00$4,850.00 -



$4,390.00$4,290.00 -



$4,000.00$3,900.00 -



$4,000.00$3,900.00
Top rated products
-



-



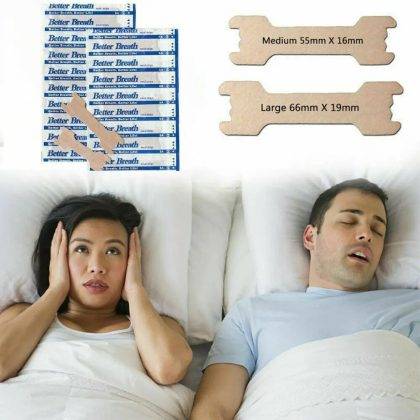
$5.94$2.94 -



$556.00$467.00 -



$4.03$3.71
On Sale Products
All Products
-




$1,780.00$6.39 -



$75.00$65.00 -



-



Products
-




$1,780.00$6.39 -



$25.00$0.09 -



$8,765.00$31.48 -



$2,500.00$2,000.00